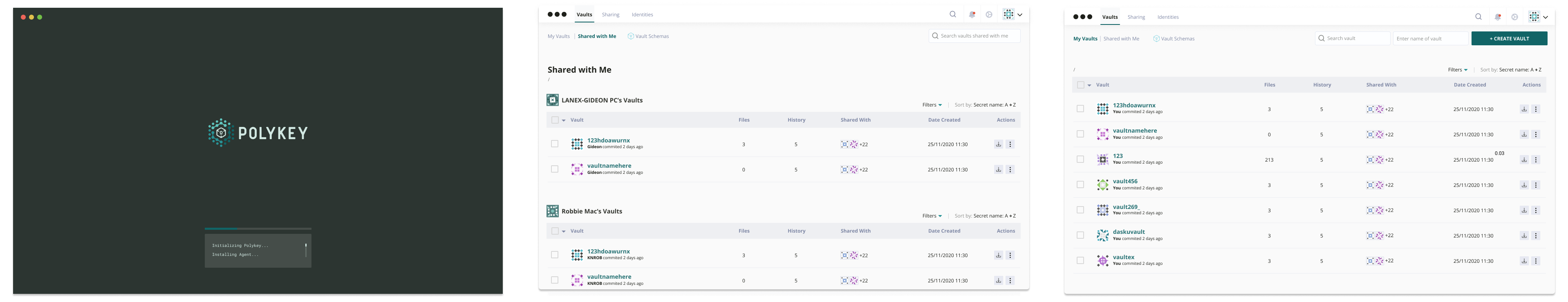
Polykey (polykey.io) is an open-source decentralized peer-to-peer secret sharing system designed to manage secrets, passwords, and API keys for humans and machines.
Secrets Management
Have you ever of experienced the headache of sharing API keys through Slack? We believe that storing and sending secrets should be simple, but not at the the cost of security and sovereignty over your data. We built Polykey to be the only secrets management solution designed to:
- Establish secure communication between decentralized trusted identities enabled by our Gestalt identity system combining Web of Trust (WoT) and Public Key Infrastructure (PKI).
- Eliminate secret sprawl with Polykey as framework for managing all types of secrets (passwords, API keys, tokens, certificates) and interoperate between any kind of secret workflow (CLI, Desktop GUI, API, Browser, Cloud Orchestration, CI/CD).
- Implement principle of least privilege across people, teams and machines with fine-grained access control.
- Track, revoke, rotate and audit secret usage across all Polykey instances.
- Fully decentralized. Maintain ownership and control over your data. No third parties, no risk of centralised data breaches, and privacy-aware.
- Support modern asymmetric and symmetric encryption, decryption, signatures and password hashing through Libsodium.
- Manage your entire organization's Polykey deployment with the Polykey enterprise control plane.
Polykey ensures that your secrets stay secret. To learn more about Polykey,
- Visit the official Polykey website at polykey.io for more information.
- Check us out on GitHub
- Or follow us on Twitter at @PolykeyIO
- Learn more at the Polykey Documentation
Matrix OS
Matrix is an operating system designed for the next era of cloud and internet of things. Its primary objective is to orchestrate massive distributed infrastructure so that they become self-healing, self-organising, and self-adaptable. The Matrix OS is comprised of 5 subsystems that interact in a feedback loop: Forge, Emergence, Overwatch, Adaptation, Convergence.